Nearly four years since Apple introduced Lockdown Mode, the company asserts that no device activated with these additional security measures has been successfully hacked.
“We are not aware of any successful mercenary spyware attacks against a Lockdown Mode-enabled Apple device,” stated Apple spokesperson Sarah O’Rourke to TechCrunch on Friday.
This is Apple’s latest confirmation that its devices with Lockdown Mode can resist government spyware, following a similar statement a year after the feature’s launch.
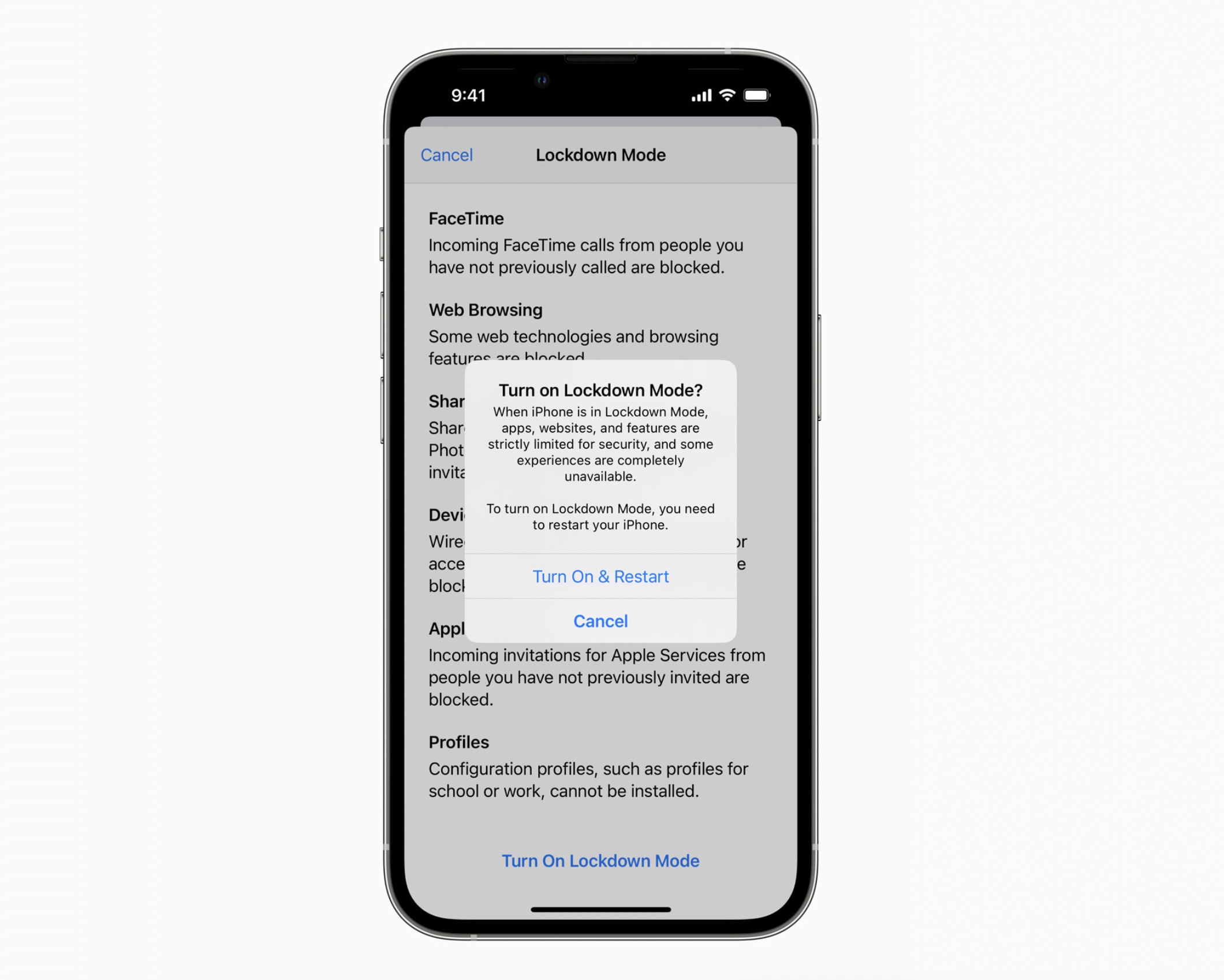
Apple announced Lockdown Mode in 2022 as an optional set of security protections that disable certain features on iPhones and other Apple devices that are often vulnerable to spyware attacks. It was specifically introduced to protect high-risk users from government spyware threats from companies such as Intellexa, NSO Group, and Paragon Solutions.
In recent times, Apple has acknowledged that its devices are susceptible to spyware. The company has become more diligent in informing users who might be targeted.
Apple has issued numerous notifications to users in over 150 countries, alerting them about potential spyware attacks, highlighting the visibility Apple now has concerning such threats. Although Apple hasn’t disclosed the number of users notified, it is assumed to be in the dozens or more.
Organizations like Amnesty International and Citizen Lab at the University of Toronto have identified several successful attacks on iPhone users, none involving a breach of Lockdown Mode. In at least two incidents, Citizen Lab mentioned Lockdown Mode effectively prevented spyware from infiltrating devices, including those attacks involving NSO’s Pegasus and Predator spyware, now under Intellexa.
In documented cases of spyware trying to attack iPhones, Google security researchers noted that the spyware would abort attacking the device if it detected Lockdown Mode, likely to avoid detection.
Apple cybersecurity expert and critic Patrick Wardle described Lockdown Mode as a crucial feature that challenges spyware developers trying to compromise Apple devices.
“Lockdown Mode is one of the most aggressive consumer-facing hardening features ever shipped,” he told TechCrunch.
Wardle noted that by “shrinking the attack surface,” Lockdown Mode removes many strategies typically exploited on iPhones, compelling spyware developers to employ more complicated and costly methods.
“It eliminates entire delivery mechanisms/exploit classes,” he added, “as it blocks most message attachment types, restricts WebKit features. This is a substantial decrease in the remotely accessible attack surface, especially for zero-click exploit chains,” referring to attacks that target users online without requiring any action from the victim.
There is a possibility that Lockdown Mode could be bypassed without detection. Nonetheless, Apple’s recent statement represents a noteworthy milestone for Lockdown Mode.
Having used Lockdown Mode for several years, I hardly think about it—except when notifications appear that can sometimes be puzzling. Some disabled features require additional steps, like copying and pasting links from messages to the browser. For these reasons, both I and other digital security experts recommend that individuals concerned about spyware or digital attacks enable Lockdown Mode.