This event mirrors a real-life Silicon Valley episode, reminiscent of an HBO satire. Recently, a severe malware incident was uncovered in an open-source project by Y Combinator graduate LiteLLM.
LiteLLM provides developers with access to numerous AI models and features like spend management. It’s a rising star, with downloads reaching up to 3.4 million times a day, as noted by Snyk, one of the security researchers tracking the issue. The project garnered 40K stars on GitHub, with numerous forks.
The malware discovery was made by Callum McMahon, a research scientist from FutureSearch, a company offering AI agents for web research. The malware infiltrated through a “dependency”—other open source software used by LiteLLM—stealing credentials and gaining access to more packages and accounts.
The malware triggered McMahon’s computer to shut down after downloading LiteLLM, prompting his investigation. Notably, a bug in the malware caused his machine to crash. This poorly designed code led McMahon and Andrej Karpathy, a renowned AI researcher, to conclude it was haphazardly coded.
LiteLLM’s developers have been diligently working to address the problem, which was detected quickly, likely within hours.
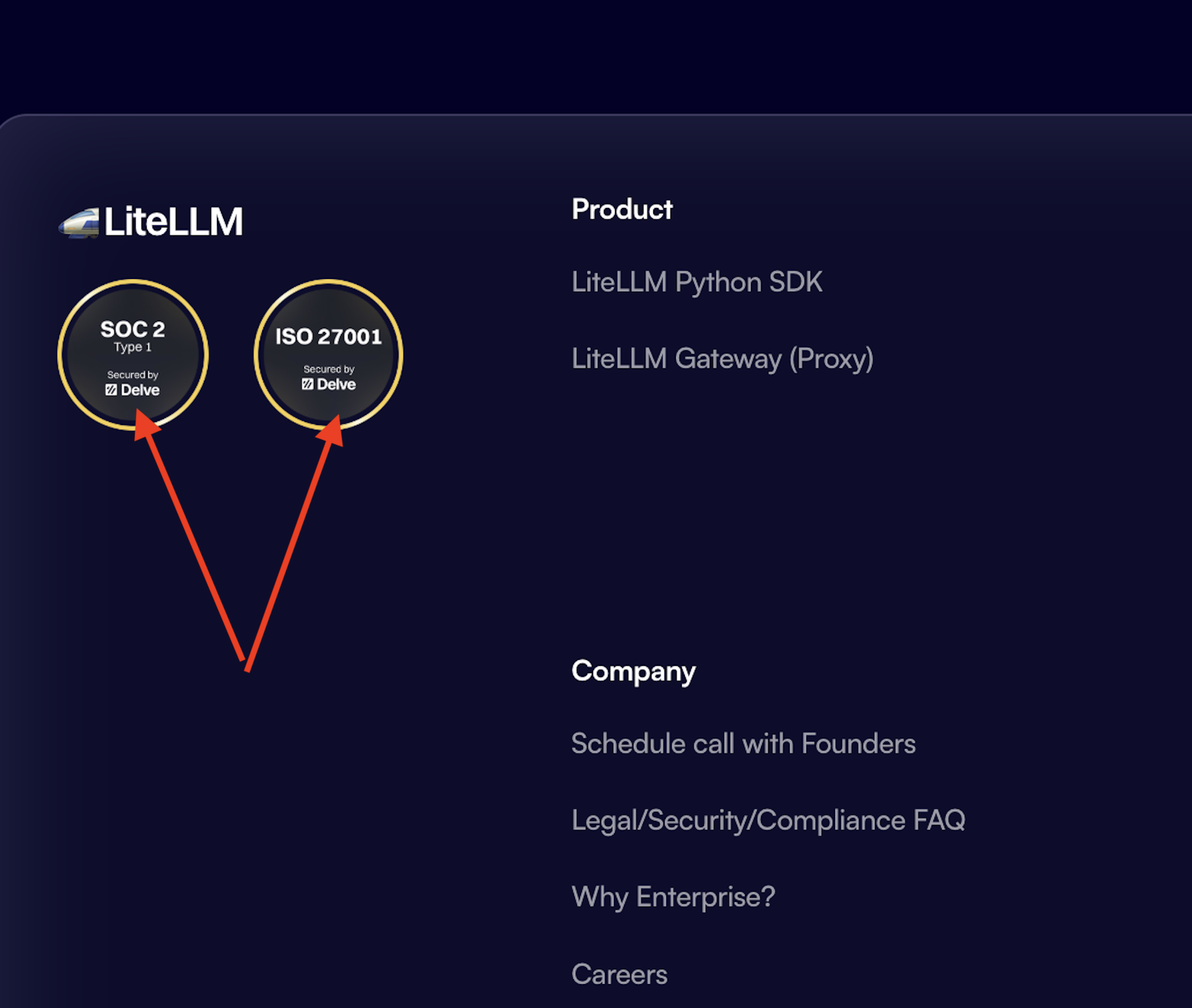
Meanwhile, onlookers on X noted that, as of March 25, LiteLLM proudly displayed on its website two major security compliance certifications, SOC2 and ISO 27001, achieved through a startup called Delve.
Delve, a Y-Combinator AI-powered compliance startup, has faced allegations of misleading customers about its compliance legitimacy through fake data generation and rubber-stamped reports, which Delve has denied.
A key point to note is that such certifications are designed to demonstrate strong security policies that help prevent incidents like this. However, certifications alone cannot immunize a company like LiteLLM from malware attacks. Although SOC 2 addresses policies around software dependencies, malware can still slip through.
Engineer Gergely Orosz remarked on X, “Oh damn, I thought this WAS a joke. … but no, LiteLLM *really* was ‘Secured by Delve.’”
LiteLLM’s CEO Krrish Dholakia refrained from commenting on the use of Delve, being focused on resolving the attack damages.
“Our current priority is the active investigation alongside Mandiant. We are committed to sharing the technical lessons learned with the developer community once our forensic review is complete,” he told TechCrunch.