The FBI has seized and dismantled two websites associated with the pro-Iranian hacktivist group, Handala, which recently claimed responsibility for a cyberattack on U.S. medical tech giant Stryker. On Thursday, the website where Handala showcased its hacks and another site that exposed individuals allegedly connected to the Israeli military and contractors like Elbit Systems and NSO Group, displayed a banner indicating law enforcement action.
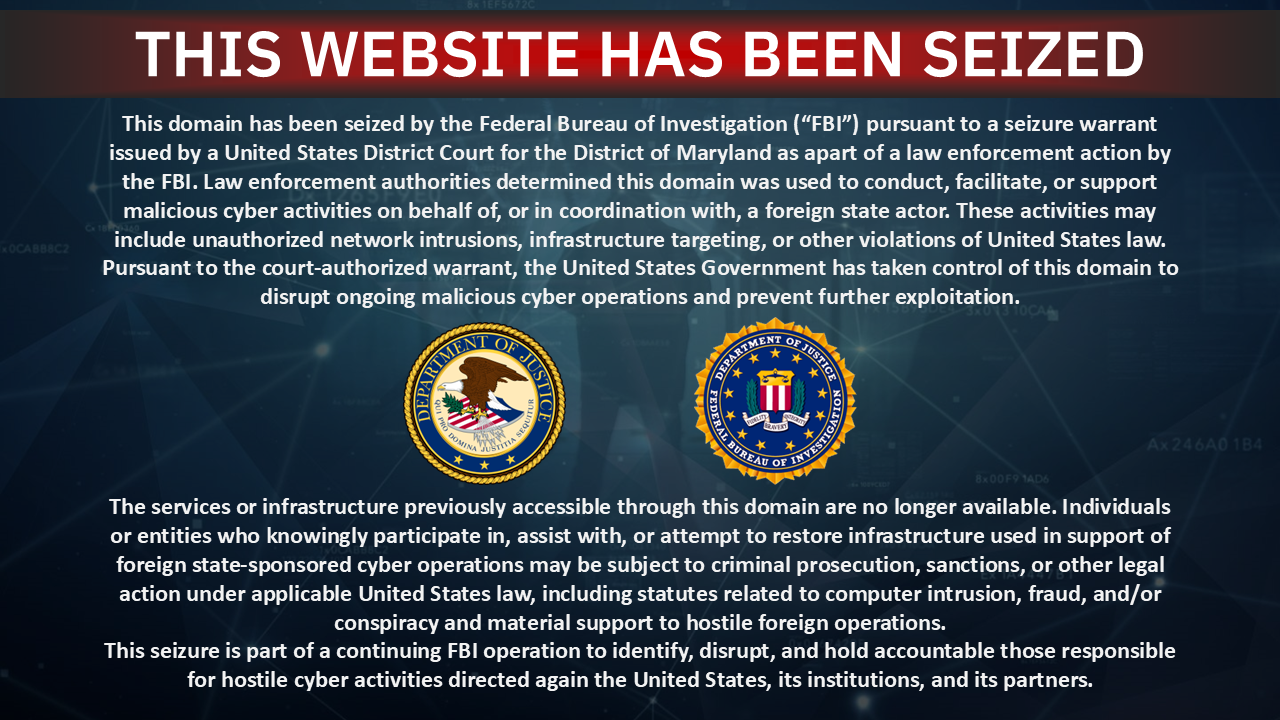
The seizure notice lacked specific reasons for the takedown by the FBI and the Justice Department, but it suggested these sites were operated by hackers with foreign government ties. It stated, “Law enforcement authorities determined this domain was used to conduct, facilitate, or support malicious cyber activities on behalf of, or in coordination with, a foreign state actor.” The U.S. government has taken control to disrupt ongoing malicious cyber operations.
TechCrunch verified the website seizures by checking nameserver records directing to FBI-controlled servers. The FBI and Justice Department did not immediately respond to TechCrunch’s request for comments.
In reaction to the seizures, Handala posted on their official Telegram channel, criticizing the action as an effort to stifle their message. They asserted that such measures only highlight the impact of their mission and the movement for truth will continue to grow.
Handala’s X account has been suspended, and they did not reply to a chat inquiry. The group has been active since the October 7, 2023, Hamas attacks and is thought to have Iranian regime connections. They claimed the attack on Stryker was a response to a U.S. missile strike in Iran.
Last year, Stryker formed a $450 million contract with the Department of Defense. Handala reportedly exploited an internal Stryker admin account, gaining extensive access to its Windows network, potentially wiping devices through Intune dashboards.
Stryker is still in the process of restoring its systems and network after the attack. Nariman Gharib, a U.K.-based Iranian activist and cyber-espionage expert, noted that while the takedowns are beneficial, activities may continue and leaks could be disseminated through media associated with the IRGC.