Four decades on, ’80s-style science fiction adventures continue to exert their influence on modern film and TV. The idea of a group of kids teaming up to face an otherworldly threat has become a trope at this point, seen in everything from Super 8 to Stranger Things. So on one level, The Boroughs, a new […]
Musk vs. Altman: A Lot of Fuss Over Nothing
Today Iâm talking with Liz Lopatto, who spent the last month covering the Musk v. Altman trial in all its chaos. Youâll hear her describe the courthouse as a âzooâ and explain that there were protests of one kind or another happening outside every day. Both Elon Musk and Sam Altman are big personalities, and […]
The Best Cases for the Switch 2 After Extensive Testing
You might find it kind of sad to put your hard-earned Switch 2 into a protective case. To me, itâs freeing. Sure, it can take away from the slick design. But using a case relieves me of the worry that the console will accumulate tons of little scratches, or worse. Iâve tested several types of […]
Wayve’s Autonomous Technology Coming to Stellantis Cars in the U.S.
Wayve’s self-driving tech will show up in Stellantis vehicles in 2028.
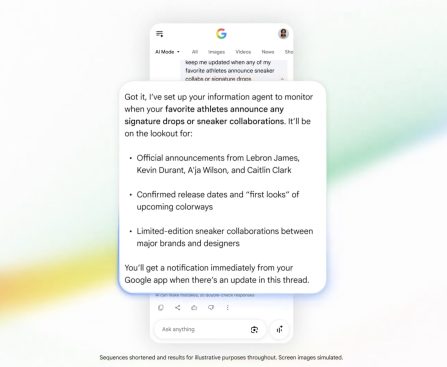
Google Pitches AI Agent Ecosystem to Reluctant Consumers
The AI agents are coming. A lot of them.
Maka Kids Redefines Screen Time with a Well-Being Focused Streaming App
Maka Kids is building a streaming app for children ages zero to six featuring content designed for healthy development. The startup has now raised $3 million in seed funding to scale its platform.
reComputer RK3576/RK3588 Edge AI Computers Now Supported by reComputer AI Lab’s One-Click Deployment Platform

Seeed Studio has just launched the reComputer RK3576/RK3588 Edge AI computers designed for developers, embedded AI innovators, robotics, industrial AI, vision AI, local LLMs, and real-world edge deployment. Rockchip RK3576 and RK3588 computers are pretty common these days, and the Seeed Studio models offer triple video output, dual Ethernet (GbE or 2.5GbE), several USB ports, and M.2 expansion. But the most interesting part is probably the software with Armbian-based Linux OS and support for the reComputer AI Lab platform that enables one-click deployment of AI-accelerated computer vision, audio, and LLM/LVM demos. reComputer RK3576/RK3588 specifications: SoC (one or the other) Rockchip RK3576 Octa-core CPU – 4x Cortex-A72 cores at 2.2GHz, 4x Cortex-A53 cores at 1.8GHz GPU â ARM Mali-G52 MC3 GPU NPU â 6 TOPS (INT8) AI accelerator with support for INT4/INT8/INT16/BF16/TF32 mixed operations. VPU Video Decoder: H.264, H.265, VP9, AV1, and AVS2 up to 8K at 30fps or 4K at […]
The post reComputer RK3576/RK3588 Edge AI computers are supported by reComputer AI Lab one-click deployment platform appeared first on CNX Software – Embedded Systems News.
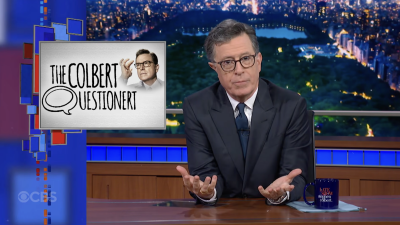
Stephen Colbert Grilled by 15 Celebrity Guest Hosts
With “The Late Show” ending, Stephen Colbert has finally taken the “Colbert Questionert” himself.
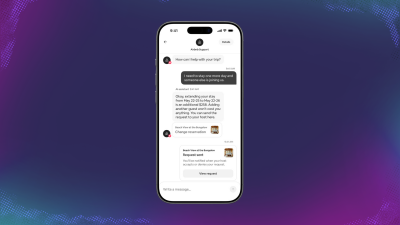
Airbnb Introduces Luggage Storage, Boutique Hotels, and AI Voice Mode
Airbnb announced additions for its app, including luggage storage, car hire, boutique hotels, and voice mode for its AI assistant.
From Selection to Access: Naseej Enhances Collection Development at Mohammed Bin Rashid Library with an Integrated Model
As part of an ongoing strategic partnership, Naseej continues to empower Mohammed Bin Rashid Library through an integrated collection development model that ensures high-quality resources, efficient management, and sustainable knowledge impact.
The post From Selection to Access: Naseej Advances Collection Development at Mohammed Bin Rashid Library Through an Integrated Model appeared first on Naseej For Technology.