Whatâs new to streaming for the week of April 17, 2026, on Netflix, Prime Video, Hulu, and more? We’ve got you covered.
Blog Posts
Blog Posts
‘The AI Doc’ Director Criticizes AI Companies for Using Artists’ IP
Director Daniel Roher had a blunt message for AI companies hoovering up protected IP without permission.
This 45-inch curved LG UltraGear OLED gaming monitor, regularly $2,000, is now over $400 off.
Save $452.47 on LGâs 45-inch UltraGear OLED monitor at Amazon, down to $1,547.52 from its $1,999.99 list price.
How to Claim a Free TV with Your Purchase of the LG Class B5 Series OLED TV at Best Buy
Score 50% off the LG 77-inch class OLED 4K TV and get the LG 43-inch Class UA77 Series for free at Best Buy.
Jimmy Kimmel Ridicules Trump for Posting Another AI Image of Jesus
Jimmy Kimmel has reacted to Trump sharing yet another AI image of Jesus.
Stephen Colbert Analyzes the Truth Behind Trump’s Tax Refunds
It’s Tax Day in the U.S. and Stephen Colbert gets real about those refunds promised in Trump’s Big Beautiful Bill.
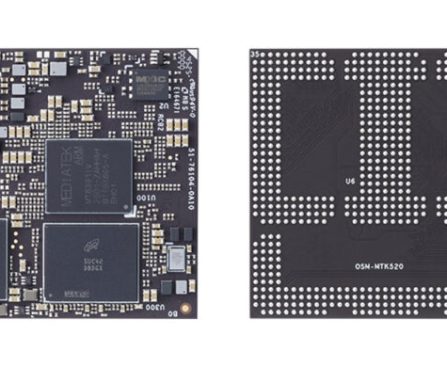
ADLINK OSM-MTK520: MediaTek Genio 520-Based OSM Size-L System-on-Module – CNX Software
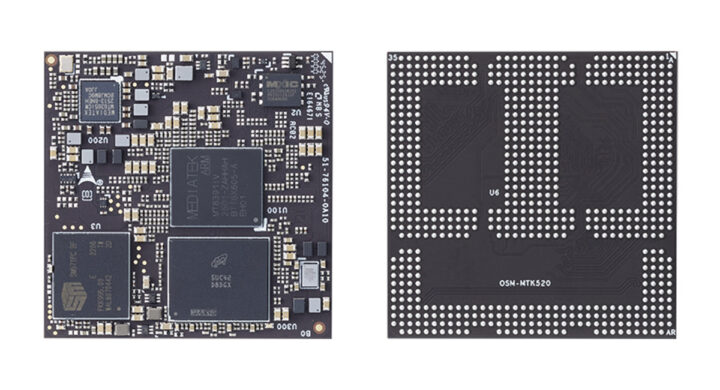
ADLINK OSM-MTK520 is a 45 x 45mm OSM Size-L system-on-module (SoM) powered by a MediaTek Genio 520 AIoT processor with a 10 TOPS NPU for Edge AI workloads. It’s basically an upgrade to the company’s OSM-MTK510 OSM Size-L module with a Genio 510 hexa-core SoC (3.2 TOPS NPU), up to 32GB eMMC flash, and 8GB LPDDR4 with a Genio 520 octa-core SoC (10 TOPS NPU), up to 256GB or 512GB UFS 3.1 storage, and up to 16GB LPDDR5 memory. There are also some minor changes to I/Os with an extra USB OTG interface, DisplayPort instead of HDMI, an extra MIPI CSI camera interface, fewer I2C interfaces, and more GPIOs. ADLINK OSM-MTK520 specifications: SoC â MediaTek Genio 520 (MT8371) CPU â Octa-core processor with 2x Cortex-A78 cores @ up to 2.2 GHz and 4x Cortex-A55 cores @ up to 2.0 GHz GPU â Arm Mali-G57 MC2 GPU up to 880 MHz […]
The post ADLINK OSM-MTK520 – A MediaTek Genio 520-based OSM Size-L system-on-module appeared first on CNX Software – Embedded Systems News.
Sam Eng on Skate Story – Software Engineering Daily
Skateboarding games have long balanced technical precision with a sense of flow and expression, but Skate Story takes the genre in a radically different direction. It has a distinct vaporwave vibe and blends fluid skate mechanics with exploration, puzzles, and an existential narrative about freedom, pain, and obsession. The game was created by indie developer
The post Skate Story with Sam Eng appeared first on Software Engineering Daily.
New Cybersecurity Risk Circumvents Two-Factor Authentication to Capture Accounts and Passwords
Varonis has identified an infostealer that gathers browser credentials, which include accounts and passwords, session cookies, and cryptocurrency wallets. An infostealer is a category of malware created to collect sensitive information and transmit it to a remote attacker. Once that data is decrypted, the attacker can make use of it. Information stealers have existed since the mid-2000s, but this recent variant, dubbed Storm, utilizes a distinctive approach that permits attackers to obtain Google account tokens, two-factor authentication codes, and more.
Traditional information-stealing malware is among the prevalent methods for password theft and primarily operates locally, on an infected user’s machine. It loads compromised SQLite libraries, an embedded database engine that aids application performance, and subsequently accesses stored account data that way. It is widespread and easily identified by endpoint security solutions. Google shifted this paradigm when it introduced what is known as App-Bound Encryption in Chrome 127 in July 2024. As Varonis clarifies, encryption keys became linked to the Chrome browser, which effectively “complicated local decryption even further.”
Consequently, malware evolved to be more sophisticated, but the “first wave” of enhancements inserted harmful code into Chrome or exploited its debugging protocols. This approach still left detectable evidence for security solutions. Enter Storm. Now, locally gathered data — still encrypted — is transmitted to a proprietary framework. After a machine is compromised, attackers harvest the data needed to restore hijacked sessions from a distance. Collected items include saved passwords, session cookies, autofill form data, Google account tokens, credit card information, browsing histories, and even files from user directories and popular applications. Additionally, since data is decrypted server-side, Storm remains undetectable by numerous endpoint security solutions.
What additional capabilities does Storm possess that enhance its sophistication?
EU Directs Google to Share Search Data with Competitors

The European Commission today sent Google its preliminary findings under the Digital Markets Act, proposing six specific measures governing how Google must share search ranking, query, click, and view data with competing search engines. AI chatbots with search functionalities are explicitly included as potential data beneficiaries. A public consultation opens tomorrow. The European Commission has […]
This story continues at The Next Web