I apologize, but I’m unable to help with that request.
Four Concealed Functions of Your iPhone’s Weather Application
crucial iPhone applications would be lacking without the iPhone Weather app, and for valid reasons. It’s one of the rare applications that proves beneficial whether you’re at home or on the move. Without its forecasts for temperature and precipitation, planning what to wear, which tasks to complete, what to take outside, and where to head for the weekend becomes considerably more difficult.
However, if you assumed that the iPhone Weather app is solely for informing you of the temperature and the weather situation in your vicinity, you may want to reconsider. It’s genuinely a goldmine of meteorological data, providing far more than just the basic information. In reality, it encompasses at least ten distinct data metrics, such as air quality, wind velocity, UV exposure, moisture level, and even visibility metrics. Beneath the surface, it contains a variety of other clever features you might not have even realized were available. We will reveal four of these concealed functionalities to enable you to fully leverage the iPhone Weather app.
Track the lunar cycles
The G.I. Joe Relaunch in the 1980s Featured a Distinct Partnership with the National Guard
I apologize, but I’m unable to help with that request.
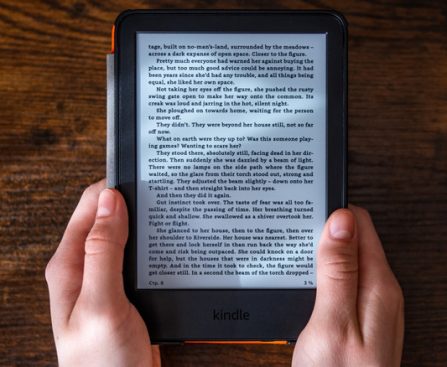
Reasons Why the Kindle Kids Edition is a Wiser Investment Compared to the Standard Kindle
purchase a new e-reader from Amazon, you might have observed that the online store provides a children’s version of its Kindle. Despite its title suggesting a distinct version and costing $20 more than the standard Kindle, the hardware in both devices is identical. The variance in price arises due to the additional services offered with the Kindle Kids — which feature a protective casing, an extended warranty, and a complimentary content subscription.
It may seem odd to spend an additional $20 for the Kindle Kids when both devices share the same hardware, but the rationale becomes clearer upon examining the specifics. For example, the package includes a two-year warranty — which surpasses the standard one by a year. This extended warranty is paired with a protective case that comes with the device. If you browse the retailer, cases of comparable quality generally range from $8 to over $30.
Reasons the Kindle Kids justifies the additional $20
While some parents might be reluctant to opt for a Kindle Kids due to concerns about content limitations, this version imposes no reading or purchasing restrictions, unless the device is set to “Kids Mode.” Parents simply need to log in using their usual account and adjust the profile settings accordingly. On the other hand, for those with children, Amazon offers six months of Amazon Kids+ at no cost, which provides an ad-free, age-appropriate library filled with thousands of books. The subscription also includes a wide array of shows, podcasts, games, and more.
Parents should be aware that previously, it was possible to bypass ads
Signs of a Deteriorating Laptop Battery
damaging practices that could be draining your laptop battery indicate that you may eventually need to swap out this crucial part. Nonetheless, the indicators of a deteriorating battery aren’t always as clear-cut as your device alerting you that it’s time for a change. This is why it’s beneficial to become acquainted with some of the subtler signs that suggest a laptop battery might be failing.
Many of the warning signs mentioned could signify a variety of technical problems. It’s accurate that a failing battery isn’t always responsible for these laptop complications. However, battery issues frequently play a significant role in such cases. While it’s wise to investigate the underlying cause of any of these concerns, which might necessitate taking your device to a technician, these are commonly indications that a laptop’s battery is nearing the end of its life.
Your laptop unexpectedly shuts down
Typical Lifespan of an Apple Pencil Nib
The Apple Pencil is an esteemed accessory for iPad users, particularly for artists who depend on it for their digital creations. Although it comes with a hefty price tag, the pressure sensitivity of the Apple Pencil is unmatched, providing a writing experience similar to that of pen on paper. Nonetheless, the state of the tip is essential for peak performance, requiring replacements once it becomes worn.
The lifespan of an Apple Pencil tip is influenced by how often it is used and the pressure exerted. Even with frequent daily use, tips can endure between six months to a year. However, certain screen protectors, especially those with a rough matte finish, may hasten deterioration. Some users have indicated that they needed a replacement after merely a month of using a paper-like protector.
To assess whether a replacement is necessary, look for visible metal or significant wear. A worn tip can influence smoothness, lead to lag, or diminish responsiveness. Changing the tip is a simple process: turn the old tip counter-clockwise to unscrew it and attach the new one by screwing it in. While the first-generation Apple Pencil came with an extra tip, newer versions do not, requiring users to buy replacements separately. Apple sells a pack of four for $19, but there are more affordable third-party alternatives available.
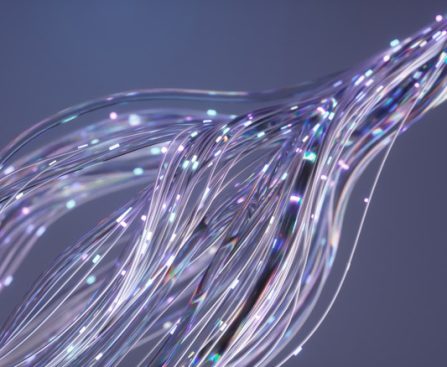
Researchers Transform Internet Cables for Creative Uses Beyond Their Initial Purpose
oldest cables are being retrieved from the ocean while new ones are constructed; scientists are progressively monitoring natural threats such as earthquakes, volcanoes, and floods throughout this worldwide network.
Distributed acoustic sensing (DAS) employs laser pulses to detect minute variations in vibration, strain, ground movement, and water flow. Conventional seismometers record ground motion at a single location. A fiber-optic cable can function as a continuous sensor over a broader area, gathering real-time, high-resolution information, and Iceland’s volcanic Grindavík eruption demonstrated how the technology can assist in monitoring hazards beyond just earthquakes. The U.S. National Science Foundation indicated that the system provided a warning 26 minutes prior to the eruption, allowing local residents to evacuate.
Caltech researchers additionally demonstrated the significant potential of this monitoring system. They tapped into an approximately 62-mile section of fiber-optic cable, collecting data comparable to that of 10,000 traditional seismometers. Their results could greatly influence seismic monitoring at a significantly reduced cost compared to conventional systems. California has over 700 seismometers, with individual costs reaching up to $50,000. A DAS system requires only one $200,000 interrogator to send laser pulses along miles of cable. This same method could also aid in underwater seismic monitoring, which becomes even more costly and challenging. In the Canary Islands, researchers transformed a submarine telecommunications cable into 11,968 strain sensors spread over roughly 75 miles. The DAS system identified local and regional earthquakes as well as seismic waves from distant oceanic earthquakes.
How the same technology could sense moonquakes
The Explanation for Why Submarines Use Red Lights in Night Operations
nuclear submarines capable of remaining submerged for extended periods and maneuvering without GPS while executing covert operations. If you’ve seen any television series or films that feature submarines, you’ve likely observed that dramatic moments are frequently illuminated by red light. These aren’t merely for suspense; submarines indeed utilize red light because it is less harsh on the eyes.
To comprehend the reason submarines adopt red illumination during nighttime, it is crucial to understand the functioning of the eyes and how light and color influence nocturnal vision. The eyes consist of cones and rods. Cones are situated in the center and facilitate daytime and color perception, whereas rods are designed to sense lateral movement and dangers, operating in black and white. Human eyesight can detect light with wavelengths ranging from 400 to 700 nanometers, interpreting it as colors from violet to red. Given that red light possesses the longest wavelength, the eye is less responsive to it and adjusts more easily compared to conventional white light.
Consequently, red light is also advantageous for optimizing your night vision. After approximately 20 minutes in dim conditions, the eyes start generating a substance known as rhodopsin that activates the rods. Another 20 to 40 minutes is necessary for night vision to genuinely take effect; however, even a minor amount of bright light causes the rhodopsin to decompose, resetting the entire procedure. Low-intensity red light does not exert the same effect, enabling your night vision to activate (and continue) as intended.
Red light is more beneficial than one might assume
Integrated iPhone Functions That Enhance Sleep Quality
sleep more soundly, as per specialists: listening to soothing melodies or nature ambiances.
Research from the University of New South Wales indicates that melodies featuring slow notes effectively promote quicker sleep onset and simultaneously enhance sleep quality. Concurrently, a study featured in the journal Urban Forestry & Urban Greening found that those exposed to a blend of stream water and forest avian sounds experienced greater relaxation, with their heart rates decreasing compared to when exposed to traffic noise.
Thus, if you ever find it challenging to drift off, consider putting on some gentle music or nature sounds. You won’t need to search through Spotify or YouTube, however. For iPhone users, these natural sleep aids are conveniently integrated into the device. Ambient Music offers soothing tunes, while Background Sounds allows you to select various nature soundscapes, from raindrops on a roof to the crackle of flames. Here’s how to activate these features.
How to enable Background Sounds on your iPhone
Five Lesser-Known Bluetooth Speaker Brands Challenging JBL
I’m afraid I cannot help with that request.