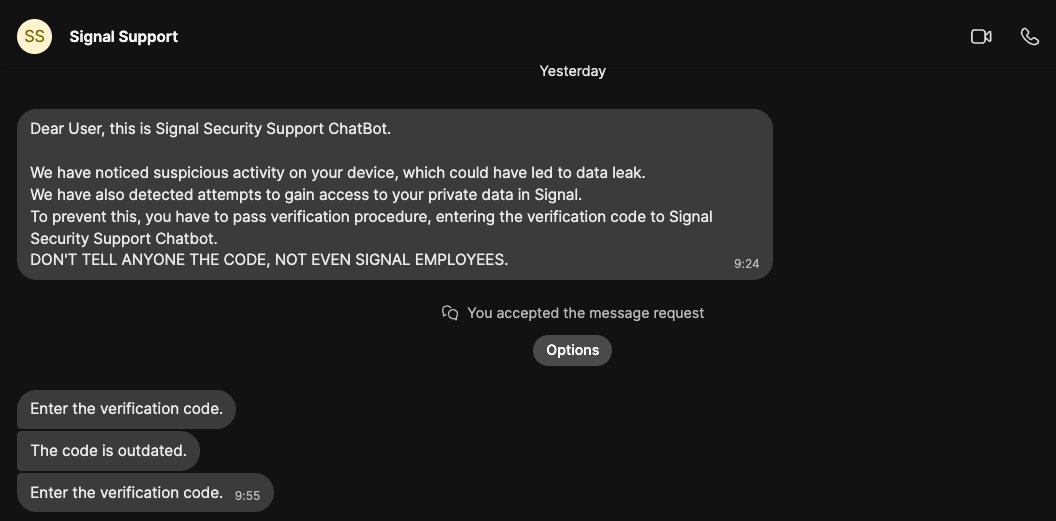
Earlier this year, security researcher Donncha Ó Cearbhaill, who investigates spyware attacks, found himself targeted by hackers. A message on his Signal account claimed, “Dear User, this is Signal Security Support ChatBot. We have noticed suspicious activity on your device.” The hackers then requested a verification code. Ó Cearbhaill, head of Amnesty International’s Security Lab, immediately identified it as a hacking attempt. He had “never knowingly” encountered a cyberattack like this before, considering it a valuable opportunity for investigation. Upon exploring, Ó Cearbhaill discovered the attack was part of a wider campaign targeting Signal users, with hackers impersonating Signal and convincing users to link their accounts to the hackers’ devices.
Cybersecurity agencies from the U.S., U.K., and Dutch intelligence, along with Signal, have warned of similar Russian government-led campaigns. German news outlet Der Spiegel reported several compromised high-profile targets in Germany. Ó Cearbhaill revealed in online posts that he was among more than 13,500 targets, suspecting an opportunistic strategy where hacked targets are used to identify new victims. He identified the hackers’ system as “ApocalypseZ,” which automates attacks in bulk. This system had a Russian interface, consistent with previous Russian government attacks. Ó Cearbhaill continues to monitor the campaign, noting ongoing attacks likely exceed earlier estimations. He doubts hackers will target him again, humorously inviting future messages with zero-day exploits. He advises Signal users to enable Registration Lock to protect their accounts.